Turn Compliance into a Clear Advantage
Security and compliance assessments based on real IT environments, helping organizations identify risk, meet regulatory requirements, and prepare confidently for audits.
Regulatory Alignment & Risk Safeguard
Keep your business aligned with global laws, frameworks, and standards to protect systems, data, and operations from legal penalties and compliance gaps.
Review your IT environment against relevant regulations and industry requirements.
Apply compliance controls that match your business model, sector, and risk exposure.
Reduce audit findings through structured documentation and governance checks.
Continuous Monitoring & Compliance Assurance
Ensure ongoing standards adherence with proactive monitoring, audits, and real-time checks that prevent violations before they escalate into operational or financial risk.
Track compliance status continuously to identify issues before they become violations.
Monitor access, data handling, and system activity to meet regulatory expectations.
Stay audit-ready with consistent records, logs, and compliance evidence.


Policy, Training & Process Integration
Build clear internal policies and train teams to sustain compliance as part of daily operations. Strengthen accountability, reduce human error, and enhance governance.
Develop clear, practical policies aligned with current compliance obligations.
Train employees to understand their role in maintaining compliance and security.
Integrate compliance checks into daily operations and change workflows.
Compliance framework we support
We help organizations prepare for audits and assessments aligned with NIST, SOC 2, HIPAA, PCI DSS, ISO 27001, and CMMC by closing gaps, documenting controls, and maintaining ongoing compliance readiness.






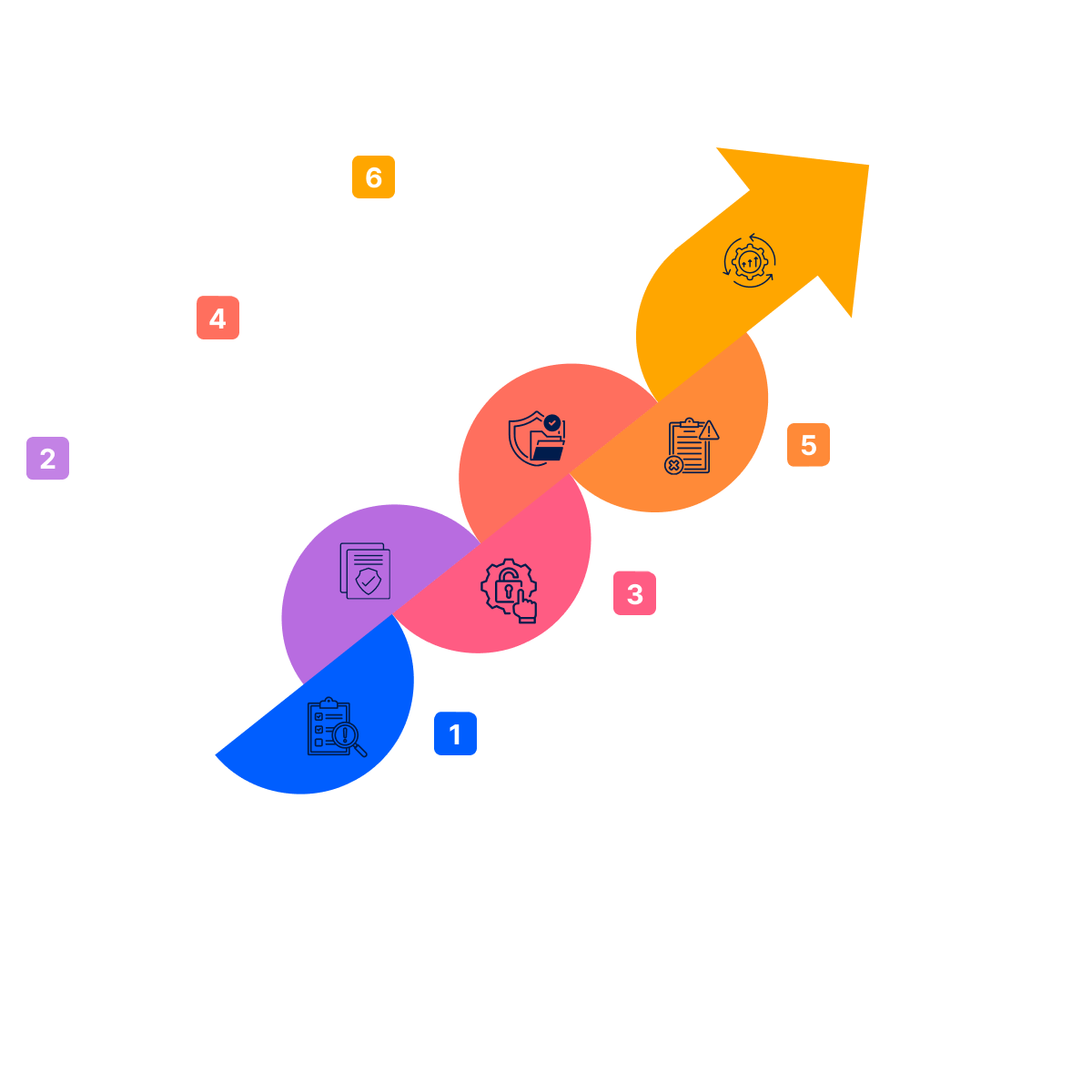
Steps to compliance confidence
Assess & Scope
We evaluate your systems, data, and regulatory exposure to define what compliance applies and where real risk exists.
Build & Align
We put the right controls, policies, and processes in place to align your environment with required compliance frameworks.
Manage & Monitor
We maintain continuous oversight, evidence, and reviews so compliance holds up over time—not just during audits.
What clients say about us
Downtime isn’t an option. Our reputation is our most valuable asset and we can not afford Ransomware. Emry Networks has secured our network and I now sleep at night.
Emry Networks exceeded our expectations with their thorough cybersecurity solutions. The Dark Web scan they provided gave us peace of mind knowing our sensitive data is protected. Highly recommend their services!
Our previous IT provider could never resolve the IT issues we experienced, and it felt like I was on the phone with them daily trying to work through problems. Emry Networks took the time to identify the root causes, and now our IT systems just work seamlessly. I couldn’t recommend them enough!
We were impressed by Emry Networks’ expertise in IT security. Their team quickly identified vulnerabilities in our system and implemented effective solutions. Our business is now better equipped to handle cyber threats.
Get audit ready now
Schedule your compliance readiness assessment with our team today.
Questions?
Find answers about our approach to securing your environment
IT compliance ensures your technology systems, policies, and safeguards meet applicable legal and regulatory requirements. It protects sensitive data, reduces legal and financial risk, and strengthens operational stability and customer trust.
Applicable standards depend on the type of data you handle, your industry, contractual obligations, and geographic location. Healthcare providers, law firms, financial services, and organizations processing credit cards each face different regulatory requirements.
A structured compliance assessment evaluates your policies, technical controls, access management, and documentation to determine whether you meet required standards and where gaps exist.
Non-compliance can result in regulatory fines, legal exposure, increased cyber insurance costs, operational disruption, reputational damage, and loss of client or patient trust.
We compare your current systems, configurations, policies, and user practices against the specific regulatory framework that applies to your organization. This reveals measurable gaps and prioritizes remediation based on risk and business impact.
Yes. Most data protection regulations apply regardless of company size when sensitive information is involved. Smaller organizations are often targeted because they lack formal safeguards, making compliance even more critical.
Formal compliance reviews are typically conducted annually, but security controls, user access, and risk exposure should be monitored continuously to prevent drift and reduce audit pressure.
It enforces structured access controls, system monitoring, encryption, documented procedures, and accountability measures that reduce the likelihood of unauthorized access, data loss, or regulatory violations.
Yes. We organize documentation, validate controls, conduct readiness reviews, and ensure evidence is properly maintained so your organization can approach audits with clarity and confidence.
Cybersecurity implements the technical safeguards that protect your systems and data. Compliance ensures those safeguards meet legal, regulatory, and contractual requirements. Together, they reduce risk while supporting business growth and long-term stability.
Need more clarity?
Reach out and we'll walk through your specific situation